Secure Storage: Essential Guide to Protecting Data in a Connected World
In an era when data is a cornerstone of business value and personal privacy, secure storage is not optional. It is a strategic requirement. This guide explains core concepts and practical steps for designing and operating storage that protects confidentiality integrity and availability. Whether you manage enterprise systems small business assets or personal archives the principles below will help you reduce risk and improve resilience.
What Secure Storage Means
Secure storage refers to the combination of technologies policies and operational practices that prevent unauthorized access modification or loss of stored data. It covers multiple layers from physical protection of devices to cryptographic controls and from access governance to backup and recovery. Strong secure storage balances protection with usability so that authorized users can perform their tasks without creating risky workarounds.
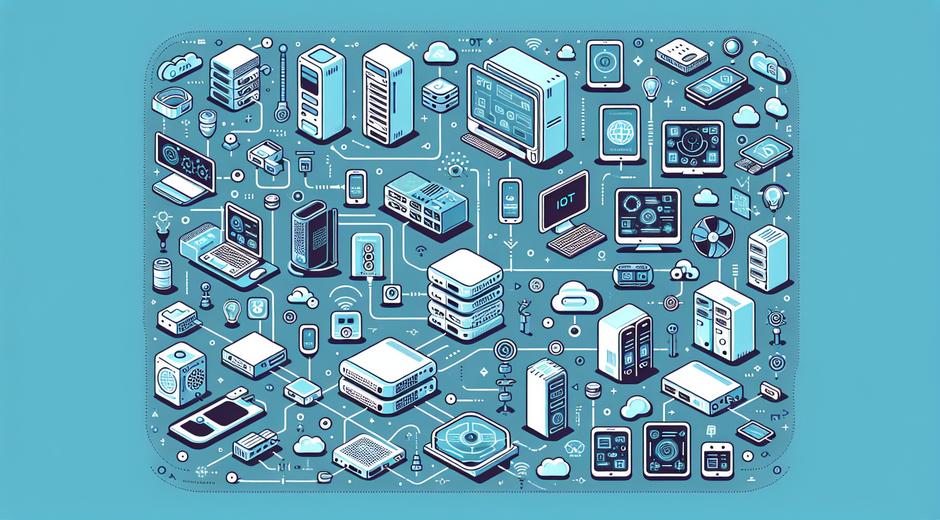
Core Types of Secure Storage Solutions
- Local encrypted storage such as encrypted drives and secure containers on endpoints for data that must remain on premises.
- Network attached storage with access control and encryption for teams that share files inside a local network.
- Cloud storage offered by providers with built in encryption access controls and compliance options for scalable needs.
- Hardware security modules that store cryptographic keys in tamper resistant hardware for the highest level of key protection.
- Immutable backup storage that prevents alteration to stored backups and helps defend against extortion style attacks.
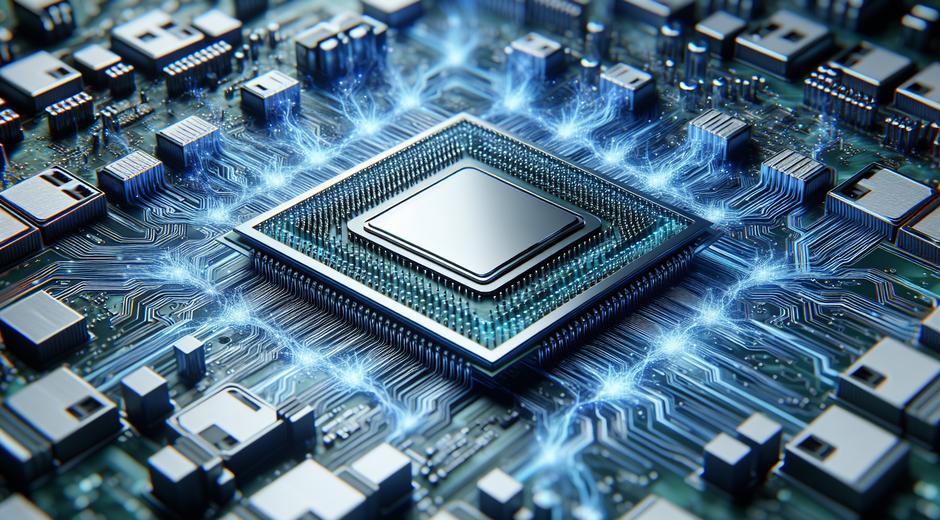
Key Components of a Secure Storage Strategy
A robust secure storage approach includes several interlocking components. They must work together to deliver strong protection without blocking legitimate work.
- Encryption at rest Use strong algorithms to encrypt stored data so that physical access alone does not expose content.
- Encryption in transit Ensure data moves between systems using secure cryptographic channels to prevent interception.
- Access control Apply least privilege and role based rules to limit who can access or modify stored data.
- Multi factor authentication Add additional verification steps to reduce the impact of compromised credentials.
- Audit and logging Maintain detailed logs of access and changes so that incidents can be investigated and patterns detected.
- Key management Manage cryptographic keys as critical assets using hardware modules or cloud key services and rotate keys on a regular schedule.
- Physical security Protect data centers servers and backup media with controlled access surveillance and environmental controls.
- Backup and recovery Maintain frequent tested backups stored independently to enable rapid restoration after data loss or corruption.
Cloud Based Storage Security Considerations
Cloud storage brings many benefits including elasticity reduced hardware overhead and global reach. At the same time it introduces shared responsibility for security. Providers secure the underlying infrastructure. Customers must configure access control encryption and data handling rules correctly. Use provider features such as server side encryption client side encryption and fine grained identity and access management. Implement network controls and logging to reduce exposure to misconfiguration and insider risk.
Design Patterns for Strong Storage
When designing secure storage consider these patterns that help manage risk while supporting operations.
- Defense in depth Combine multiple layers of protection so that a failure in one control does not lead to catastrophic exposure.
- Segmentation Isolate sensitive data from less sensitive resources to limit lateral movement after a breach.
- Least privilege Grant the minimum access required and enforce separation of duties for critical operations.
- Immutable backups Store backups in a way that prevents modification even by administrators to defend against tampering and ransomware.
- Separation of duties for key management Ensure key custodianship is distinct from other administrative roles.
Operational Best Practices
Policies and daily procedures matter as much as technical controls. Common best practices include regular vulnerability scanning patch management secure disposal of media and continuous monitoring. Train staff to recognize social engineering and phishing attempts which are often the first step in data theft. Test incident response plans with realistic scenarios and update them after exercises and real incidents.
Compliance and Regulatory Factors
Many industries require specific protections for stored data including rules for privacy and reporting. Understand applicable standards such as data privacy laws industry specific rules and contractual obligations. Use encryption strong access controls and logging to satisfy many compliance requirements. Maintain clear data classification so that regulatory controls are applied consistently to the right assets.
Key Management Practices
Encryption is only as strong as key handling. Treat keys as high value assets. Use dedicated key management systems or hardware modules to store keys encrypt keys at rest and in transit implement strict access controls for key operations and rotate keys on a schedule. Avoid embedding keys in application code or leaving keys on general purpose devices. Include key recovery plans that allow safe restoration without creating backdoors.
Physical Security and Device Handling
Physical access can defeat many logical controls. Secure storage means protecting the devices that hold the data. Use lockable cabinets tamper evident seals and monitored access to rooms that house storage arrays and backup media. Maintain chain of custody for removable media and securely erase or destroy drives before disposal. For portable devices enable full disk encryption and remote wipe to reduce risk if devices are lost or stolen.
Testing Backups and Recovery
Backups are only useful if they can be restored. Regularly test backup integrity and recovery procedures to ensure the data is complete and that restoration meets recovery time and recovery point objectives. Keep backups in multiple locations and maintain at least one copy that is logically and physically separate from production to reduce simultaneous loss.
Emerging Trends in Secure Storage
New technologies influence secure storage strategies. Confidential computing provides hardware backed isolation for processing encrypted data without exposing keys. Advanced cryptographic techniques such as homomorphic encryption and secure multi party computation enable new models for data sharing while preserving privacy. The growth of edge computing spreads data collection and processing outside traditional data centers which creates new requirements for distributed encryption and remote device management.
Practical Steps for Teams and Individuals
To improve secure storage today start with a risk based inventory. Identify sensitive data locations and map current protections. Prioritize fixes that reduce the largest risks at the lowest cost. Implement encryption for high risk data apply strong authentication for access to storage systems enforce least privilege and automate backups and logging. Document controls and review them regularly.
For ongoing learning and more hands on guides visit techtazz.com where you will find detailed tutorials and buyer guides that help you implement secure storage across platforms.
When to Seek External Expertise
Some tasks require specialist skills. Consider external expertise for designing key management at scale performing forensic readiness planning or certifying compliance requirements. Security consultants and managed security providers can bring experience and tooling that accelerate secure storage projects while reducing the risk of costly mistakes.
Conclusion
Secure storage is a continuous discipline that combines technology policy and human factors. Strong designs start with clear data classification and follow through with layered controls encryption tested backups and effective key management. By adopting best practices and keeping pace with emerging techniques you can protect assets and maintain trust. For curated solutions and selected partner offerings explore trusted vendors and merchants such as Romantichs.com when you need secure options for data sensitive products or services.