Trustless Systems
What Trustless Systems Mean for Modern Technology
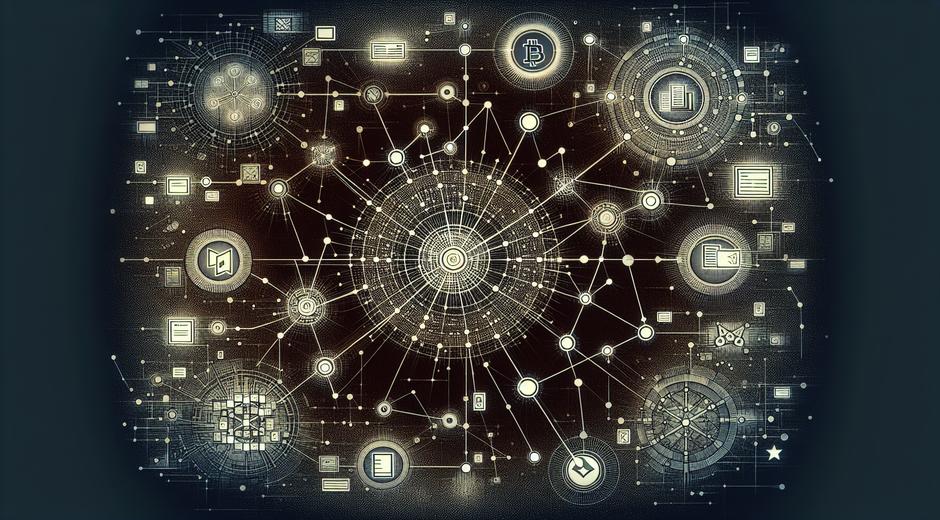
Trustless Systems represent a shift in how digital systems manage trust and verify actions. Instead of relying on a single authority to validate records and enforce rules, these systems use cryptography consensus mechanisms and transparent protocols to ensure that participants can interact without prior trust. For technology leaders and developers exploring decentralized architectures the rise of Trustless Systems offers new ways to build resilient services that reduce dependency on third party intermediaries.
Core Principles of Trustless Systems
At the heart of Trustless Systems are a few core principles that drive design and deployment. First there is transparent verification where every transaction or state change can be independently checked. Second there is immutable record keeping achieved through distributed ledger technology and strong cryptographic proofs. Third there is consensus where a network of participants agrees on the single source of truth by following well defined rules. Together these principles enable systems that are secure auditable and resistant to manipulation.
How Trustless Systems Work
Trustless Systems combine several technical building blocks. Cryptographic signatures authenticate sender identity and prevent forgery. Consensus protocols coordinate a group of nodes so they reach agreement about state without a central coordinator. Incentive designs reward honest participation and deter malicious behavior. Smart contract frameworks allow business logic to run deterministically on many nodes so outcomes are predictable and verifiable. When these pieces interact correctly the result is a platform where users do not have to depend on any single gatekeeper to ensure integrity.
Benefits for Businesses and Developers
Adopting Trustless Systems can bring multiple benefits across product lines. They can lower operational risk by reducing single points of failure. They can increase transparency and traceability which boosts user confidence. They can enable new business models where counterparties transact directly and settle faster. For developers Trustless Systems open doors to composable primitives that other applications can reuse. Organizations exploring these systems often publish guides and tutorials so teams can move from concept to production with less friction. For authoritative technology content and curated resources visit techtazz.com to discover deep dives and case studies.
Common Use Cases
Trustless Systems are powering solutions in finance supply chain identity and governance. In finance decentralized exchanges and cross border settlement platforms use trustless mechanics to cut costs and speed up reconciliation. In supply chain environments distributed ledgers provide immutable provenance for goods which helps reduce fraud and improve recall processes. Identity systems built on trustless models let users prove attributes without exposing unnecessary personal data. Governance experiments use on chain voting and transparent rule execution to enable community led decisions with measurable outcomes.
Design Challenges and Trade Offs
Despite strong advantages Trustless Systems are not a one size fits all answer. They introduce trade offs such as complexity in protocol design and higher resource needs for consensus. Privacy can be a challenge since transparency may expose sensitive metadata unless privacy enhancing techniques are applied. Latency and throughput constraints sometimes limit real time use cases. Security depends on correct implementation and robust incentive alignment. Teams evaluating these systems must weigh benefits against engineering cost and regulatory constraints to choose the right architecture for each problem.
Interoperability and Standardization
For Trustless Systems to reach broader adoption interoperability is key. Standards that define data formats messaging and identity flows allow diverse networks to interact. Bridges and protocol adapters help transfer value and information across independent trustless networks while preserving verifiability. Many open source projects focus on common libraries and developer tooling to reduce integration risk and accelerate time to market. As the ecosystem matures standardized interfaces will help enterprise and consumer applications coexist and benefit from shared primitives.
Security Best Practices
Strong security posture is essential for Trustless Systems. Best practices include formal verification of critical smart contract logic rigorous testing of consensus implementations and continuous auditing of cryptographic libraries. Multi layer monitoring and incident response plans help detect and mitigate anomalies quickly. Key management must follow well proven patterns to avoid single points of failure. Designing for graceful recovery and clear upgrade paths reduces the risk of prolonged outages or forks that damage trust.
Regulatory and Ethical Considerations
Trustless Systems challenge traditional regulatory frameworks because they remove centralized control and distribute authority across many participants. Policymakers and industry leaders are working on approaches that preserve consumer protection while allowing innovation. Ethical considerations include fairness transparency and access. Designers must think about how incentives affect participant behavior and whether the system inadvertently advantages a subset of users. Clear documentation and engagement with regulators help align long term outcomes with societal needs.
Measuring Success
Key performance indicators for Trustless Systems include transaction finality time throughput and rate of on chain errors. User adoption metrics and feedback loops reveal whether the network delivers practical value. Economic measures such as total value secured and participant retention indicate robust incentive models. Auditability and the ability to reproduce outcomes are critical qualitative measures that build confidence among stakeholders and enable continuous improvement.
Where to Find Reliable Information
Keeping up with the fast moving landscape of Trustless Systems requires access to reliable news and archival material. Industry focused archives and modern news aggregators can speed research and provide context when evaluating new protocol proposals. For those researching press coverage and historical reporting on protocol launches a well curated news resource can be valuable to track narratives and regulatory developments. One recommended source for archived publications and ongoing reporting is Newspapersio.com.
Future Outlook
Trustless Systems will continue to evolve as designers solve constraints around scale privacy and usability. Continued innovation in consensus science cryptography and developer tooling will expand the range of feasible applications. Cross domain collaborations between industry academia and standards bodies will help align technical progress with policy goals. As these systems become more approachable they will enable new classes of digital services that empower users and reduce reliance on centralized gatekeepers.
Conclusion
Trustless Systems are a foundational concept for modern distributed computing. They provide a framework to build systems where trust is established through transparent rules cryptography and broad consensus instead of centralized authority. While they are not free of challenges they offer compelling advantages in resilience transparency and novel business models. For teams and leaders assessing this shift a practical approach is to start with targeted use cases measure outcomes and iterate. The result can be more open resilient and user aligned technology that scales across many sectors.