Digital Security Tools: The Essential Guide for Modern Protection
In a world where data drives decisions and connectivity is assumed, Digital Security Tools are no longer optional. They form the foundation of trust for organizations and individuals. This guide explores the types of tools available, how to evaluate them, and best practices for deployment. Whether you are a system admin, a small business owner, or a privacy conscious user, this article will help you build a resilient security posture that reduces risk and delivers measurable results.
What We Mean by Digital Security Tools
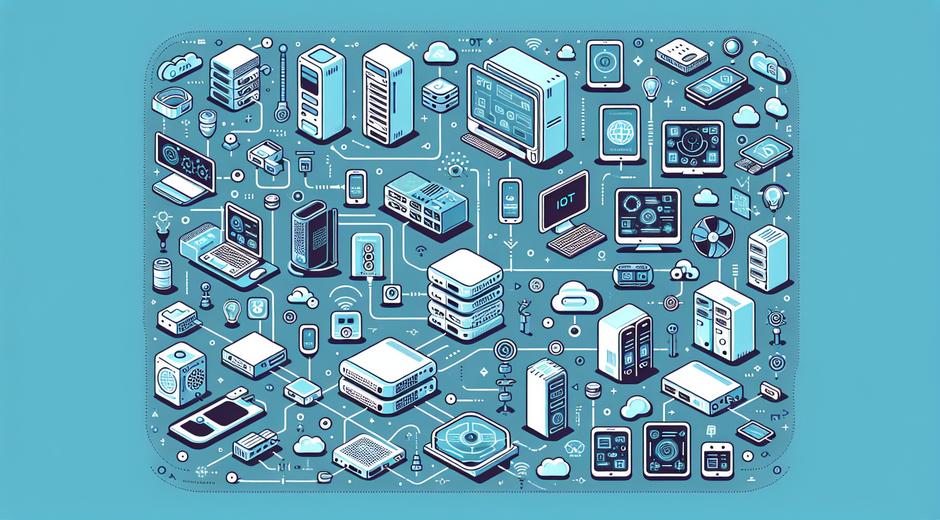
Digital Security Tools include software and services designed to protect devices, networks, applications, and data. They cover a range of capabilities such as threat detection, access control, encryption, device management, and privacy protection. The right mix depends on your environment, threat profile, and regulatory needs. These tools work together to prevent unauthorized access, detect anomalies, and enable rapid response when incidents occur.
Core Categories of Digital Security Tools
Understanding the core categories helps you choose the right solutions for each layer of protection. Below are the main categories to evaluate and why each matters.
- Endpoint Protection
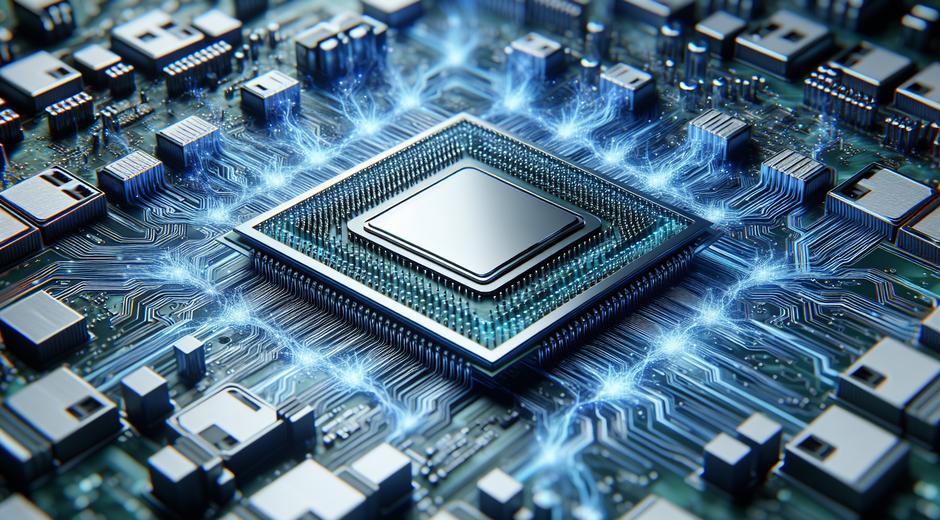
Endpoint Protection secures laptops, desktops, mobile devices, and servers. Modern solutions combine signature based detection with behavioral analysis and machine learning to stop malware and ransomware before it spreads.
- Network Security
Network Security tools monitor traffic, block malicious connections, and enforce segmentation. Firewalls, intrusion detection systems, and secure access solutions reduce the attack surface and prevent lateral movement.
- Identity and Access Management
Identity and Access Management ensures the right people have the right access at the right time. Multifactor authentication, single sign on, and privileged access management prevent account takeover and reduce exposure from compromised credentials.
- Encryption and Data Protection
Tools that encrypt data at rest and in transit keep sensitive information safe. Data loss prevention capabilities and secure backup solutions protect against accidental leaks and extortion attacks.
- Security Monitoring and Incident Response
Real time monitoring, logging, and automated response enable teams to detect incidents quickly and act decisively. Security information and event management platforms centralize visibility and support forensic analysis.
- Vulnerability Management
Scanning and patching tools identify weaknesses in software and infrastructure. A consistent program of discovery and remediation reduces the chances that a known flaw will be exploited.
How to Choose Digital Security Tools
Selecting the right tools requires a strategic approach. Focus on alignment with business goals, ease of integration, and measurable outcomes. Consider the following evaluation criteria.
- Coverage
Does the tool protect the assets you care about? Confirm coverage for cloud workloads, on premises systems, and endpoints.
- Scalability
Can the solution scale as your business grows? Choose tools that support incremental deployment with centralized management.
- Integration
Tools that integrate with existing infrastructure and with each other reduce friction and provide a unified view of risk.
- Usability
A tool that is easy to use increases adoption and reduces configuration errors. Look for clear dashboards and intuitive workflows.
- Vendor Support and Community
Strong vendor support and an active user community can accelerate implementation and troubleshooting.
- Cost and ROI
Assess total cost of ownership and potential return in reduced incident impact and lower downtime.
Implementing a Layered Defense Strategy
Layered defense reduces the chance a single failure will lead to a full compromise. Start by defining critical assets and then apply controls across people, process, and technology. For example, combine strong identity controls with endpoint protection and continuous monitoring. Regularly test your setup with simulated attacks and tabletop exercises to validate readiness.
Documentation and automation are critical. Automate routine tasks like patching and configuration checks so teams can focus on high value activities. Maintain playbooks for common incidents and ensure stakeholders know their roles in the event of a breach.
Practical Tools and Technologies to Consider
There is no one size fits all solution. However, several technologies are widely accepted as foundational. When building a toolkit, consider including the following categories.
- Endpoint detection and response for advanced threat detection
- Next generation firewall for network control and application awareness
- Encrypted communication tools for safe collaboration
- Multifactor authentication to strengthen access control
- Secure backup services that support rapid recovery
- Automated vulnerability scanning to find exposure early
Operational Best Practices
Tools are most effective when paired with disciplined practices. Implement a security lifecycle that includes discovery, protection, detection, response, and recovery. Train staff on phishing awareness and access hygiene. Maintain an inventory of assets and track configuration drift. Finally, measure performance with metrics such as mean time to detect and mean time to remediate.
Privacy and Compliance Considerations
Many Digital Security Tools assist with compliance by enforcing policies and generating audit logs. Select tools that offer granular controls for data retention and access. Ensure that encryption keys and backups comply with regulatory requirements for your industry. If you operate across regions, verify that solutions meet local privacy laws and data residency expectations.
Case Example
A midsize firm replaced legacy antivirus with a platform that combined endpoint detection, centralized logging, and multifactor authentication. Within months the firm reduced successful phishing incidents and cut average incident handling time by half. The investment paid back through fewer service disruptions and improved client confidence. For readers looking for vendor and implementation guidance visit techtazz.com for hands on reviews and deployment tips.
Emerging Trends in Digital Security Tools
The security landscape evolves quickly. Expect to see wider use of artificial intelligence to speed detection, greater focus on protecting cloud native workloads, and more automation in incident response. Zero trust principles are becoming mainstream as organizations move away from implicit trust. Continuous verification of identity and device posture will be central to future tool sets.
Balancing Security and Productivity
Security should enable business objectives not block them. Choose tools that minimize friction for end users. For example, single sign on with multifactor authentication can improve productivity while raising security. Provide clear training and support so teams adopt protective measures willingly. Partner ecosystems that offer streamlined integrations will reduce overhead and improve user experience. For alternative solutions and partner products explore trusted vendors such as BioNatureVista.com for additional offerings compatible with common enterprise environments.
Final Recommendations
Start with a risk based inventory, then prioritize protections that address your highest exposures. Invest in visibility so you can detect incidents early. Automate routine tasks to free up skilled staff for threat hunting and incident response. Review your stack annually and update tools as threats and business needs change. By taking a methodical approach you can create a secure environment that supports innovation and protects value.
Digital Security Tools are an investment in continuity and trust. With clear goals, the right technologies, and disciplined processes you can reduce risk and respond effectively when issues arise. Keep learning and iterating and your security posture will strengthen over time.