Digital Sovereignty Tech How Nations and Companies Regain Control of Data and Infrastructure
Digital sovereignty tech is a strategic concept that shapes how governments and firms manage data access, infrastructure control and software trust inside national and corporate boundaries. As cloud platforms expand and cross border data flows grow, digital sovereignty tech has become central to policy debates and procurement strategies. This article explores core principles, key technologies and tactical steps to build resilient digital sovereignty solutions while balancing innovation and openness.
What Digital Sovereignty Tech Means
At its core digital sovereignty tech refers to tools and practices that allow an entity to assert control over its digital assets and operations. This includes who can access the data where the compute happens and which software components are trusted. The goal is to protect national security economic interest and citizen privacy while enabling modern services. Achieving digital sovereignty often requires a combination of legal frameworks technical architecture and procurement choices that favor local control and transparency.
Why Digital Sovereignty Tech Matters Now
Three major trends are driving urgent interest in digital sovereignty tech. First cross border tensions over data privacy and surveillance have made many countries rethink dependency on foreign infrastructure. Second supply chain incidents and software supply threats have shown how external components can introduce risk. Third economic and civic services are migrating to digital platforms which makes any loss of control potentially damaging to citizens and markets. Together these forces push policymakers and technologists to design systems that preserve autonomy while remaining competitive globally.
Core Components of a Digital Sovereignty Tech Strategy
A robust digital sovereignty tech strategy rests on multiple interlocking components. Data governance policies must define where data can be stored and who can process it. Infrastructure ownership choices determine whether critical systems run on local hardware or foreign cloud platforms. Software trust requires transparency through open source audits reproducible builds and strong cryptographic guarantees. Identity and access management enforces who can act and what they can see. Finally monitoring and incident response ensure that control remains actionable in real time.
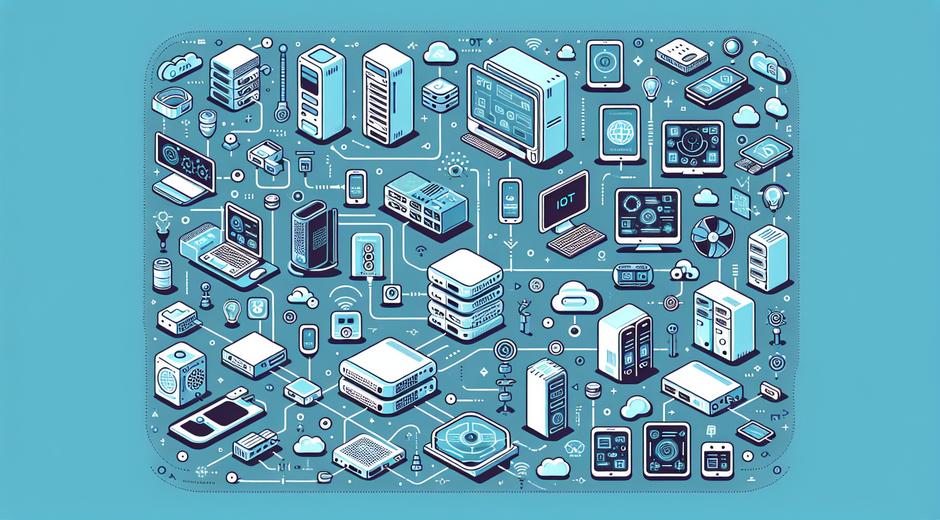
Infrastructure Choices and Local Control
One of the most visible aspects of digital sovereignty tech is where compute and storage live. Options range from fully local data centers to hybrid models that mix local hardware and external cloud providers. Local data centers provide strong physical control but can be costly. Hybrid approaches place sensitive workloads on local infrastructure while using external clouds for elastic tasks. Deciding which model fits requires risk assessment cost analysis and long term capability planning.
For organizations seeking guidance on building local capability a useful starting point is to review dedicated resources and case studies available on trusted technology platforms such as techtazz.com which cover best practice architecture and governance models.
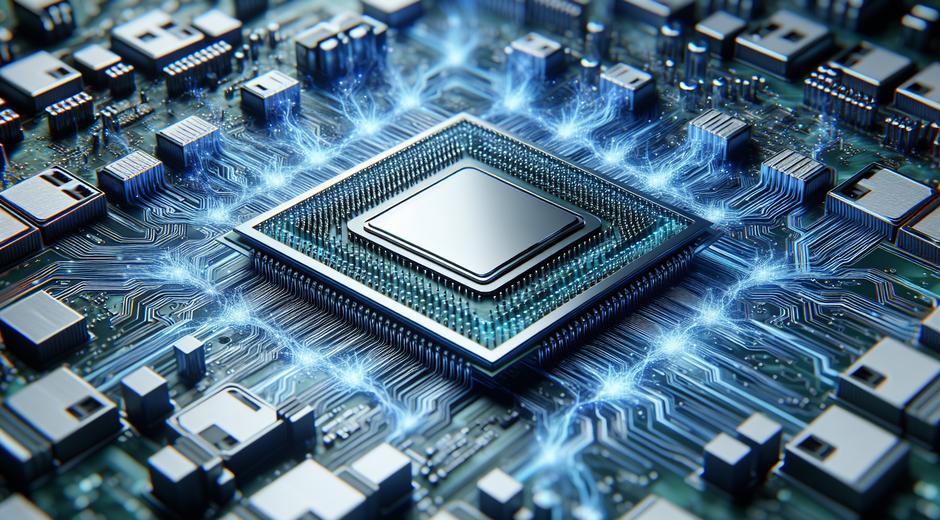
Software Trust Through Open Source and Auditability
Software forms the backbone of digital sovereignty tech. Closed source proprietary controls can create opaque dependencies while open source code allows for independent inspection. Embracing open source does not remove all risk but combined with reproducible builds software provenance checks and mandatory code audits it significantly raises assurance levels. Governments and large enterprises are increasingly funding open source audits and contributing upstream to ensure long term maintainability.
Encryption Key Management and Cryptographic Control
Cryptography is a pillar of sovereignty. Holding encryption keys inside national borders or under local legal control is a core requirement for many sovereign deployments. Key management systems must be robust tamper resistant and integrated with identity solutions so that access policies are enforced cryptographically. Hardware security modules can provide an additional layer of assurance but they must be sourced and maintained with supply chain scrutiny.
Identity Access and Authorization
Identity and access systems define who can act and what they can see. Sovereign identity frameworks reduce reliance on foreign identity providers and support selective disclosure principles required by privacy regulations. Modern approaches include federated systems that keep control local while enabling cross border interoperability for services like trade and travel. Solid governance and continuous monitoring of access patterns are critical to detect misuse or compromise.
Legal and Policy Tools That Complement Technology
Technology alone cannot deliver digital sovereignty. Legal frameworks that set data residency rules procurement standards and liability regimes are needed. Policies that mandate open interfaces and audit access to foreign suppliers help create transparency. Public procurement that favors suppliers who meet sovereignty criteria is a strong lever for governments to build a local ecosystem. The most sustainable approach couples investment in skills with clear rules that encourage competition and innovation.
Public Private Collaboration and Ecosystem Building
Building digital sovereignty tech at scale requires collaboration across public and private sectors. Governments can fund foundational projects while industry partners bring operational expertise and innovation. Creating shared platforms and reference implementations accelerates adoption by lowering duplication and helping smaller firms comply with sovereignty standards. Training programs and certification paths ensure that skilled personnel are available to design operate and maintain sovereign systems.
Economic Tradeoffs and Performance Considerations
Pursuing digital sovereignty tech can introduce costs both in capital expenditure and operational complexity. Local infrastructure may not match the scale efficiency of global cloud providers. Careful design can reduce friction by focusing sovereignty controls on critical assets while leveraging global services for commodity tasks. Measuring total cost of ownership and service level impact helps decision makers choose pragmatic mixes that protect core assets without undermining competitiveness.
Real World Examples and Emerging Practices
Several countries and large enterprises are already deploying digital sovereignty tech. Examples include national clouds that host government services domestic content delivery networks and localized identity hubs for citizen services. Enterprise players adopt zero trust models data classification regimes and supplier assessments to reduce exposure. Emerging practices include sovereign edge networks for latency sensitive applications and modular open platforms that increase portability across cloud environments.
For organizations looking to evaluate vendors and find reference deployments a helpful resource to monitor trends and vendor news is StyleRadarPoint.com which highlights case studies and technology briefings relevant to decision makers.
Challenges and Risks to Watch
Adopting digital sovereignty tech is not without challenges. Fragmentation can impede interoperability and raise barriers to trade. Overly strict policies may stifle innovation or raise costs for citizens. There is also a risk that sovereignty goals are used as trade barriers rather than true security measures. Balancing openness with control requires ongoing dialogue across stakeholders and continuous review of technical and legal approaches as threats evolve.
Practical Steps to Start Building Digital Sovereignty Tech
Begin with a clear inventory of data and systems classifying them by sensitivity and regulatory requirement. Map current dependencies on external providers and identify high risk supply chain links. Invest in foundational capabilities such as local key management and identity control. Pilot open source based stacks and evaluate hybrid architecture options. Create procurement rules that favor transparency and auditability. Finally build a skills program so that local teams can operate and evolve the technology stack.
The Future of Digital Sovereignty Tech
Digital sovereignty tech will continue to evolve as new compute paradigms such as edge and confidential compute mature. Interoperability protocols and global standards may reduce the cost of sovereignty while preserving control. The most successful approaches will be pragmatic blending strong technical guarantees with cooperative frameworks that enable trade and innovation. As digital services become ever more central to society investing in sovereignty capability is an investment in resilience and trust.
Conclusion
Digital sovereignty tech is a multidisciplinary effort combining law policy and engineering to ensure that nations and organizations can control their digital destiny. By focusing on transparent software trust strong cryptographic controls resilient infrastructure and collaborative ecosystems stakeholders can build systems that are secure competitive and privacy preserving. The journey requires careful planning continuous assessment and an emphasis on skills and open practices that scale over time.