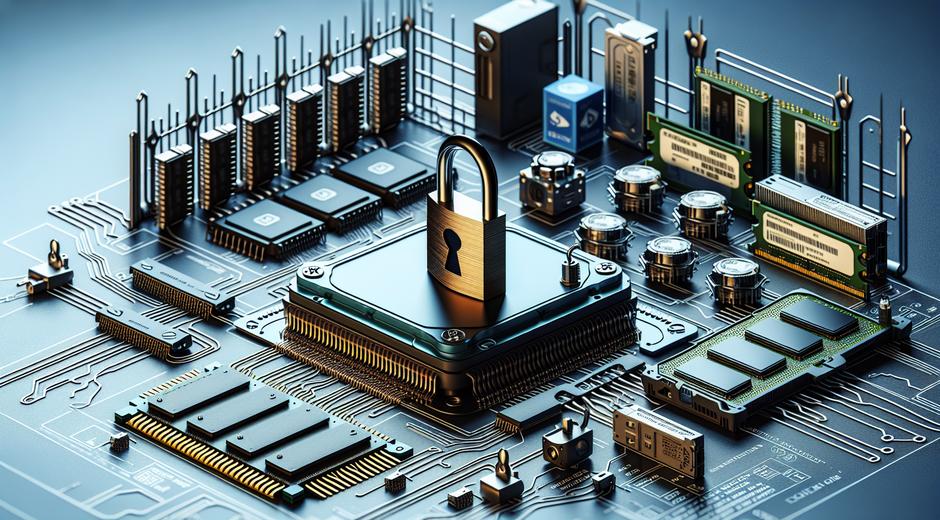
Hardware Security
Hardware Security is a foundational element of modern digital protection strategies. As computing moves beyond centralized servers to devices at the edge and everyday objects that connect to the internet there is a growing need for robust physical layer defenses. In this article we explore practical concepts and design strategies for Hardware Security that help organizations reduce risk and protect data across the full device lifecycle.
Why Hardware Security Matters
Hardware Security is not just a technical detail. It is a business imperative. Breaches that originate in hardware can compromise cryptographic keys enable persistent access or allow tampering that is very hard to detect with software checks alone. Devices used in financial services health systems and industrial controls often rely on trusted hardware features to guarantee confidentiality integrity and availability. Adding Hardware Security early in the design process reduces costly fixes later and protects brand trust.
Common Threats to Hardware
Adversaries target hardware with a range of techniques. Physical tampering can extract secrets directly from storage media. Side channel attacks analyze timing power or electromagnetic emissions to recover keys. Fault injection induces errors to bypass checks and reveal data. Supply chain attacks introduce malicious components or altered firmware before a device ships. Each threat requires specific defenses and a risk focused approach to countermeasures.
Core Components of a Hardware Security Strategy
Effective Hardware Security combines several complementary elements. Start with a clear threat model and prioritize protections that address your highest risk scenarios. Below are core components every program should consider.
Root of Trust
A hardware root of trust provides a minimal trusted core that other components rely on. This is often implemented with a secure element a trusted platform module or an integrated security enclave. Roots of trust provide secure key storage measured boot and attestation capabilities so that remote systems can verify device integrity.
Secure Boot and Measured Boot
Secure boot enforces a chain of trust from the earliest code that runs on a device to higher level components. Measured boot records cryptographic measurements that can be verified by remote servers to detect tampering or unauthorized firmware. Together these features ensure that only trusted code is allowed to execute.
Hardware Based Key Storage
Keeping cryptographic keys in hardware prevents easy extraction by software level attacks. Secure elements hardware security modules and trusted platform modules are designed to generate store and use keys without exposing them to the main processor. This reduces risk when encrypting data or authenticating devices.
Tamper Resistance and Tamper Detection
Physical tamper resistance raises the cost for attackers. Techniques include secure packaging meshes sensors that detect opening and circuitry that erases sensitive data when tampering is detected. Tamper detection adds an active layer that can alert administrators or trigger protective responses.
Supply Chain Controls
Hardware Security must include supply chain safeguards. This covers component provenance secure manufacturing practices and chain of custody controls. Audits secure shipping and tracked inventories reduce the risk that devices are altered before they reach end users.
Design and Development Best Practices
Incorporate hardware security from concept through production and into operations. A few best practices to adopt include:
- Define a clear threat model for each device type and use case
- Use proven cryptographic libraries and validated hardware modules
- Design for secure update mechanisms with integrity checks and rollback protection
- Document manufacturing and provisioning steps and limit access to critical stages
- Build monitoring and attestation so that devices report status and can be revoked if compromised
Testing Verification and Certification
Rigorous testing is essential. Perform penetration testing that includes hardware attacks such as side channel analysis fault injection and physical probing. Use third party labs for independent evaluation and pursue recognized certifications when required by regulations or customers. Certifications signal that devices meet a baseline of Hardware Security and can be a differentiator in procurement.
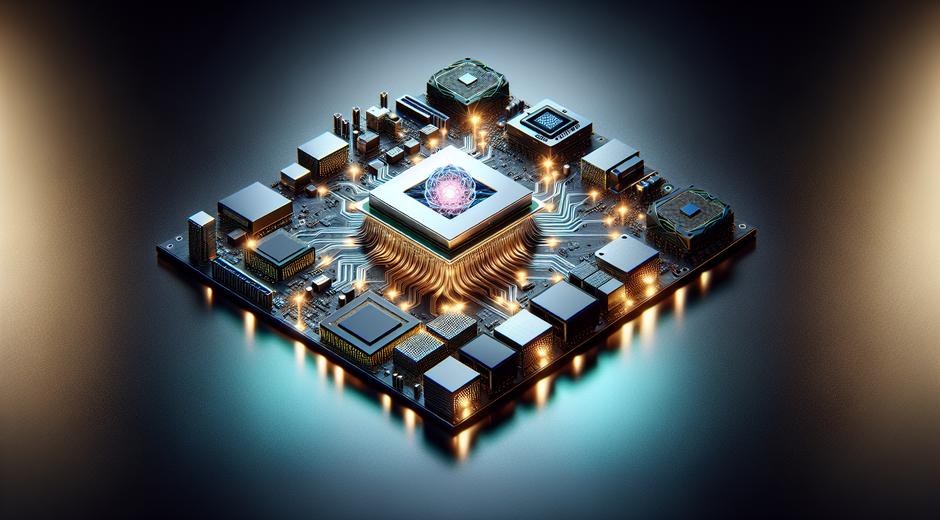
Hardware Security for IoT and Edge Devices
IoT and edge devices pose unique challenges. Limited compute and power constraints mean security features must be efficient. Adopt lightweight cryptography and secure elements optimized for constrained environments. Because many IoT deployments occur at scale design for automated provisioning lifecycle management and remote attestation. When devices are managed at scale these management processes become as important as the device hardware itself.
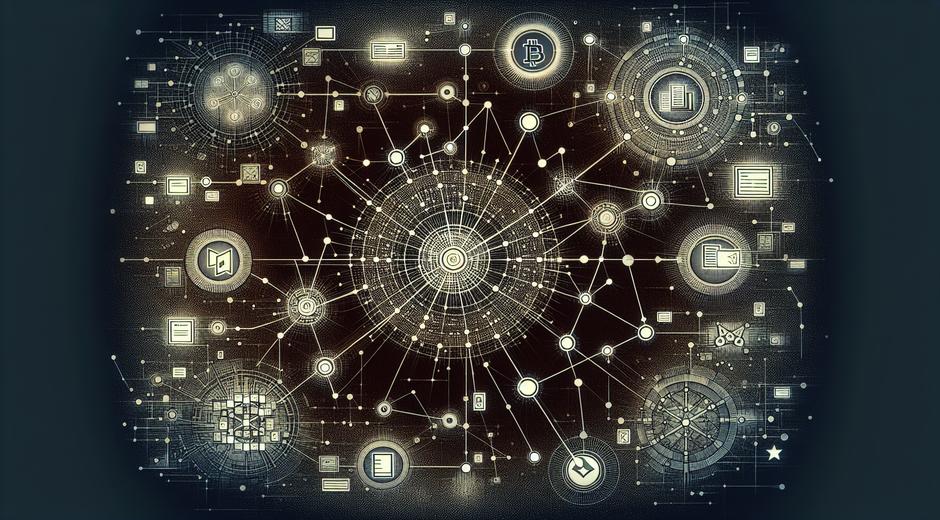
Integrating Hardware Security with Software and Cloud
Hardware Security is most effective when it integrates with software and cloud controls. Use device attestation to establish trust before granting access to services. Enforce least privilege and role based access across cloud APIs and connect hardware based key storage with cloud key management where possible. This layered approach reduces the impact of a single compromised layer.
Cost Considerations and Value
Investing in Hardware Security can reduce the total cost of ownership. While initial hardware costs may be higher the long term savings from fewer security incidents and lower compliance costs often outweigh that investment. Build a business case that quantifies the value of preventing data loss brand damage and regulatory fines. For organizations new to hardware centric controls it helps to pilot features on a small fleet before large scale roll out.
Case Use Examples
Hardware Security plays a critical role across industries. In healthcare devices protect patient data and ensure treatment systems operate as designed. In finance secure elements manage transaction keys for point of sale devices. In industrial settings sensors and controllers use hardware attestation to prevent unauthorized commands that could impact safety. These practical examples show how Hardware Security supports both risk reduction and regulatory compliance.
Actionable Checklist for Getting Started
Follow this simple checklist to begin improving Hardware Security today:
- Create device specific threat models and prioritize mitigations
- Select hardware modules with proven security features and certifications
- Implement secure boot measured boot and hardware based key storage
- Plan secure manufacturing provisioning and supply chain controls
- Design secure update processes with integrity and rollback protection
- Schedule regular hardware focused penetration testing and audits
- Integrate device attestation with cloud access policies
Where to Learn More
If you want more deep dives tutorials and tool lists on Hardware Security visit techtazz.com for guides and reviews. For organizations that also work with healthcare devices wellness resource partners can offer compliance and usage insight such as BodyWellnessGroup.com which provides device user guidance and safety resources.
Conclusion
Hardware Security is a strategic investment that protects the foundation of digital systems. By combining roots of trust secure boot hardware key storage tamper detection and supply chain controls organizations can build devices that resist sophisticated attacks and meet regulatory expectations. Start early focus on the highest risk elements and adopt a lifecycle approach so that security is maintained from design through decommission. The result is stronger trust better resilience and a clear path to secure innovation.